A few weeks ago, I saw a message on the Metasploit mailing list (which you should also join, or at least follow on seclists.org) regarding Metasploit Community Edition. The fine folks at Offensive Security have an outstanding training site covering the Metasploit Framework, but do not cover the Community Edition. While by no means is this on the same level as Metasploit Unleashed, I present to you…
Metasploit Community Unleashed
Background
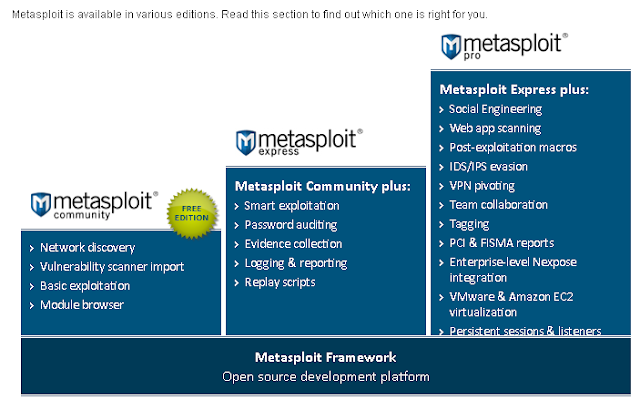
Metasploit Community Edition is a free subset of the paid versions of Metasploit available from Rapid 7. It is initendied to simplify network discovery and vulnerability verification.
Further information about this excellent project can be obtained at: http://www.rapid7.com/products/metasploit-community.jsp
To install Metasploit Community on Backtrack, simply type apt-get install Metasploit at a shell prompt. The wizards at backtrack-linux made the install seamless.
Once the install is complete, start the Metasploit web interface, by selecting the Backtrack Miscellaneous menu or /opt/metasploit/ctlscript.sh start. Metasploit Community Edition runs as a ssl web application on port 3790. On first run, you must license your copy with Rapid 7 and create a user.
Metasploit Community Edition Scanning
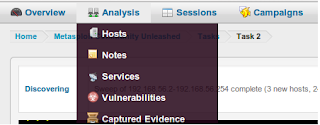
Begin by creating a new project and filling in the project name, description and network range. On the new workspace select the scan button. Enter the IP address or range to scan. Selecting Show Advanced Options allows fine grained tuning of the scan details including adding specific nmap scanning options. exclusions and timing options.